The code infusion digital assault technique can be a genuine danger to the business. This is what you have to think about taking off a code infusion assault.
Code infusion assaults, which are once in a while alluded to as remote code execution assaults, can be a genuine danger to an association's security. Curiously, in any case, the expression "code infusion assault" doesn't allude to a particular assault technique. Or maybe, it is a nonexclusive term used to portray an endeavor in which aggressors misuse ineffectively composed code in a manner that permits them to execute their own code. The more you think about this digital assault technique, the better set you up will be to fight it off in any case.
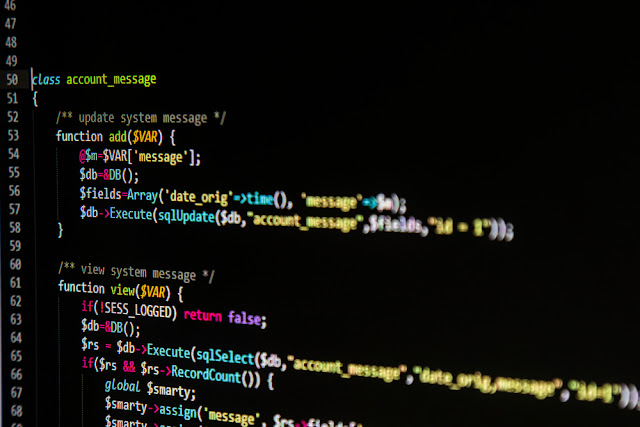
Code infusion assaults are a digital assault technique ordinarily coordinated against programming dialects, for example, PHP or Python. In any case, the basic stage is fairly insignificant since past assaults have been coordinated against a wide assortment of stages. Code infusion assaults have focused on everything from SQL Server databases to Windows PowerShell.
2.) The second thing that an aggressor needs to make a code infusion assault work is a methods for executing the directions that they go into the objective site, content or application. There truly isn't a lot of that assailants can do to compel their code to be executed, so they for the most part depend on tirelessness and a touch of karma. Aggressors may, for example, enter a similar direction into many diverse structure fields, with the expectation that one of those fields will have been built such that makes the guidance be executed.
There are three primary things that application designers must do to shield their applications from being abused by a code infusion assault.
1.) To start with, input approval is a flat out must. Set up decides that will constrain what can be gone into a field. In the event that a field is requesting that a client enter their name, for instance, at that point you may restrict the quantity of characters that can be entered and preclude the utilization of numbers and uncommon images. These means will go far toward forestalling code infusion assaults.
3.) What's more, in conclusion, altogether test your applications (counting any consequent patches). Have a go at entering benevolent directions into content fields to guarantee that the application is appropriately taking care of the information. For more, click here.
Code infusion assaults, which are once in a while alluded to as remote code execution assaults, can be a genuine danger to an association's security. Curiously, in any case, the expression "code infusion assault" doesn't allude to a particular assault technique. Or maybe, it is a nonexclusive term used to portray an endeavor in which aggressors misuse ineffectively composed code in a manner that permits them to execute their own code. The more you think about this digital assault technique, the better set you up will be to fight it off in any case.
Code infusion assaults are a digital assault technique ordinarily coordinated against programming dialects, for example, PHP or Python. In any case, the basic stage is fairly insignificant since past assaults have been coordinated against a wide assortment of stages. Code infusion assaults have focused on everything from SQL Server databases to Windows PowerShell.
Here's an extremely straightforward model from the best IT services organizations..
The specific mechanics of a code infusion assault differ broadly dependent on the stage that is being assaulted, however code infusion assaults regularly make them thing in like manner: They misuse invalidated input.
Practically all well known sites permit client made substance. A site may, for instance, permit its clients to survey an item or remark on a video. Site clients commonly enter their remarks into a book box and afterward click a submit button. After doing as such, their remark is added to the page.
At an early stage, Website proprietors found this apparently basic procedure could be abused. As opposed to entering plain content into a remark box, the individuals who had terrible plan would at times enter HTML code. By and large, locales would really assess the code, as opposed to just showing the code as plain content. Spammers once in a while utilized this method to mortar promotions (complete with pictures and huge textual styles) all over Internet remark sheets. The individuals who had vindictive purpose would now and then implant diverts into their code, in order to infect site guests with malware.
There are two principle things that are important for an advanced code infusion assault to succeed.
The specific mechanics of a code infusion assault differ broadly dependent on the stage that is being assaulted, however code infusion assaults regularly make them thing in like manner: They misuse invalidated input.
Practically all well known sites permit client made substance. A site may, for instance, permit its clients to survey an item or remark on a video. Site clients commonly enter their remarks into a book box and afterward click a submit button. After doing as such, their remark is added to the page.
At an early stage, Website proprietors found this apparently basic procedure could be abused. As opposed to entering plain content into a remark box, the individuals who had terrible plan would at times enter HTML code. By and large, locales would really assess the code, as opposed to just showing the code as plain content. Spammers once in a while utilized this method to mortar promotions (complete with pictures and huge textual styles) all over Internet remark sheets. The individuals who had vindictive purpose would now and then implant diverts into their code, in order to infect site guests with malware.
There are two principle things that are important for an advanced code infusion assault to succeed.
1.) To begin with, there must be some open door for an assailant to enter vindictive code. Keep in mind, however, the expression "code infusion assault" is a conventional term. In that capacity, there are possibly any number of ways that an assailant could enter pernicious code.
Code infusion assaults regularly target content section fields inside applications. An aggressor may, for example, attempt to enter directions into a field that requests a snippet of data, for example, a client's name or address. Remark fields are likewise a most loved potential objective.
A program's location bar is another mainstream target. Numerous sites add page-explicit parameters as far as possible of a URL. Since these parameters are on display, an aggressor may attempt to abuse them as a methods for accessing the site's back-end assets.
2.) The second thing that an aggressor needs to make a code infusion assault work is a methods for executing the directions that they go into the objective site, content or application. There truly isn't a lot of that assailants can do to compel their code to be executed, so they for the most part depend on tirelessness and a touch of karma. Aggressors may, for example, enter a similar direction into many diverse structure fields, with the expectation that one of those fields will have been built such that makes the guidance be executed.
There are three primary things that application designers must do to shield their applications from being abused by a code infusion assault.
1.) To start with, input approval is a flat out must. Set up decides that will constrain what can be gone into a field. In the event that a field is requesting that a client enter their name, for instance, at that point you may restrict the quantity of characters that can be entered and preclude the utilization of numbers and uncommon images. These means will go far toward forestalling code infusion assaults.
2.) Second, abstain from including any guidelines that could cause client contribution to be executed. On account of a PowerShell content, for example, you should abstain from utilizing the Invoke-Expression cmdlet. On account of PHP code, you ought to abstain from utilizing eval().
3.) What's more, in conclusion, altogether test your applications (counting any consequent patches). Have a go at entering benevolent directions into content fields to guarantee that the application is appropriately taking care of the information. For more, click here.

Comments
Post a Comment